New Intel CPU Kernel Memory Leaking 5-30% drop in Performance
It is being reported a new critical security vulnerability is being revealed in Intel CPUs.
The patch to fix the kernel memory leaking vulnerability will according to different benchmarks result in anywhere from 5-30% performance loss.
A new Security vulnerability discovered in Intel CPUs can cause a 5-30% Performance Hit on macOS, Windows & Linux based systems.
Intel CEO sold large amount of stock prior to exposure
Speculations arise about Intel CEO on purpose sold stock in December 2017 before disclosure.
The Intel CEO Brian Krzanich reported several transactions recently selling stock options.
This might be a sign of a red flag and could indicate prior knowledge of the vulnerability.
Krzanich is only keep the bare minimum of stocks left which is required by the CEO before the sale he had 495,743 shares.
Intel minimum number of shares requirement:
CEO: 250,000
Chairman and president: 150,000
CFO: 125,000
Vice President 100,000
Senior vice president 65,000
Corporate vice president 35,000
Other senior leaders 5,000-10,000
It could be that Krzanich sold those 245,743 shares valued $11 million to prevent loss after the vulnerability disclosure.
Performance loss for all users of Intel CPUs on macOS, Linux and Windows
The performance bug can not be fixed through BIOS or Micro Code updates.
It is only fixable at the OS level via software which will cause a huge performance loss.
The software fix for this Intel CPU problem for Linux/Windows/macOS is looking to introduce a new performance decreased for all users.
It is set to anywhere in the range from 5% to 30% depending on the tasks being done.
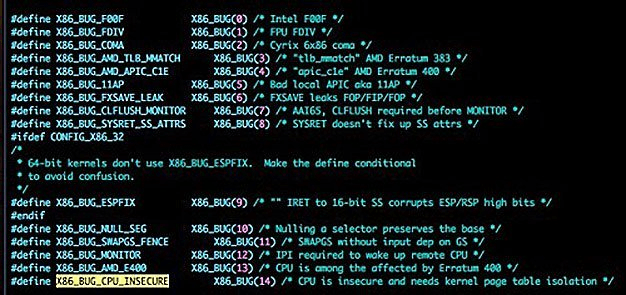
The new x86 PTI patches are included in Linux Kernel 4.15-rc6
The performance decrease depends on much the program deals with the kernel and context switching activity.
For simple user space application with less interaction the x86 PTI additions should not be notified to cause much difference.
The latest Intel CPUs with PCID will also help to ensure less of a performance decrease.
Intel Kernel Page Table Vulnerability - credit: python sweetness
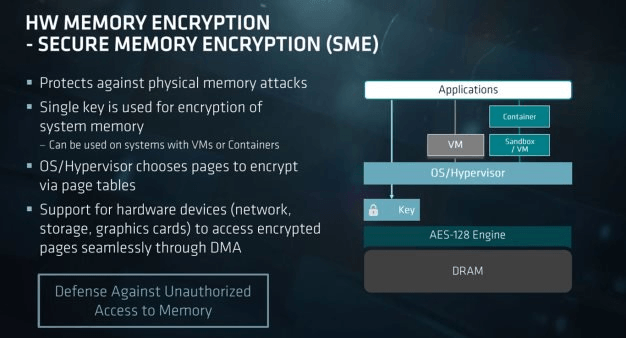
AMD CPUs not hit by any performance decrease
AMD micro processors are not known to be effected by a similar vulnerability at this moment.
This can be due to the security protection AMD processors already have deployed.
AMD Secure Memory Encryption Technology In EPYC Server CPUs
 
Which Intel CPUs are affected by Meltdown Vulnerability?
It is reported any Intel CPU post 2010 is to be affected.
Every Intel CPU processor which uses out of order execution is potentially vulnerable.
Which is every processor since 1995 except Intel Itanium and Intel Atom before 2013.
The Meltdown attack has been tested on CPUs released as early as 2011.
It is still unclear if ARM and AMD processors are vulnerable.
Some reported CPUs are:
Intel Core i7-6700 will take a 29% performance hit
And an Intel Core i7-3770S will run 34% slower.
Which system are effected by Spectre vulnerability?
Which CVE numbers are associated with the vulnerabilities?
Spectre vulnerability CVE-2017-5753, CVE-2017-5715
Meltdown vulnerability CVE-2017-5754
What is the difference between the Spectre and Meltdown vulnerabilities?
Meltdown breaks the CPU mechanism which keeps applications from getting access to arbitrary memory.
Application programs which can access memory can reveal sensitive data
Spectre vulnerability the other way tricks applications to access arbitrary locations in the memory.
Why is it called Meltdown Vulnerability?
The vulnerability bug melts the security limits and boundaries which are designed to be enforced by hardware.
Why is it called Spectre?
This is a root problem based on speculative execution and is not easy to fix.
Linux Performance Hard Hit
The first performance results on Linux based platforms have been released on the Internet.
The early numbers show that IO intensive workloads such as SQL are especially sensitive to the Kernel Page Table Isolation Patch.
This can effect large sites being hit by performance decrease and users being unable to login to sites.
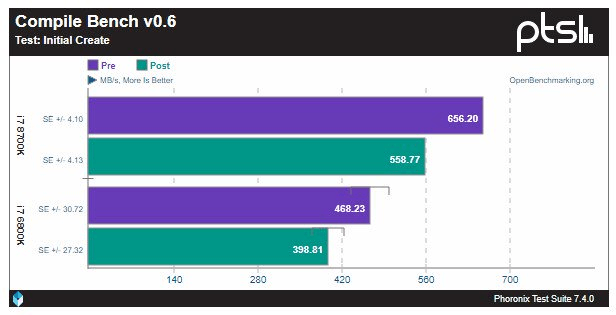
Credit: Phoronix
When will Microsoft patch Windows systems?
As reported on 3 January 2017 Microsoft to include a fix on next Patch Tuesday with KB4056892.
Gamers moving to AMD Ryzen ?
This might be what AMD has been waiting for and can cause many gamers to switch from I5, I7 based systems to AMD Ryzen CPUs.
Linux Patches
The latest Linux updates byLinus Torvalds himself are posted here https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=5aa90a84589282b87666f92b6c3c917c8080a9bf
Will the performance loss be permanent?
Unfortunately it looks as a permanent performance loss on users on Intel CPUs.
The patches that have been made now might be tweaked in the future and leave a lesser performance drop that has been shown now.
However it is certain some performance loss is to be expected permanently. |