Cloud Vulnerability Scanning Questions FAQ
Do you have a question for the Cloud Vulnerability Scanner service?
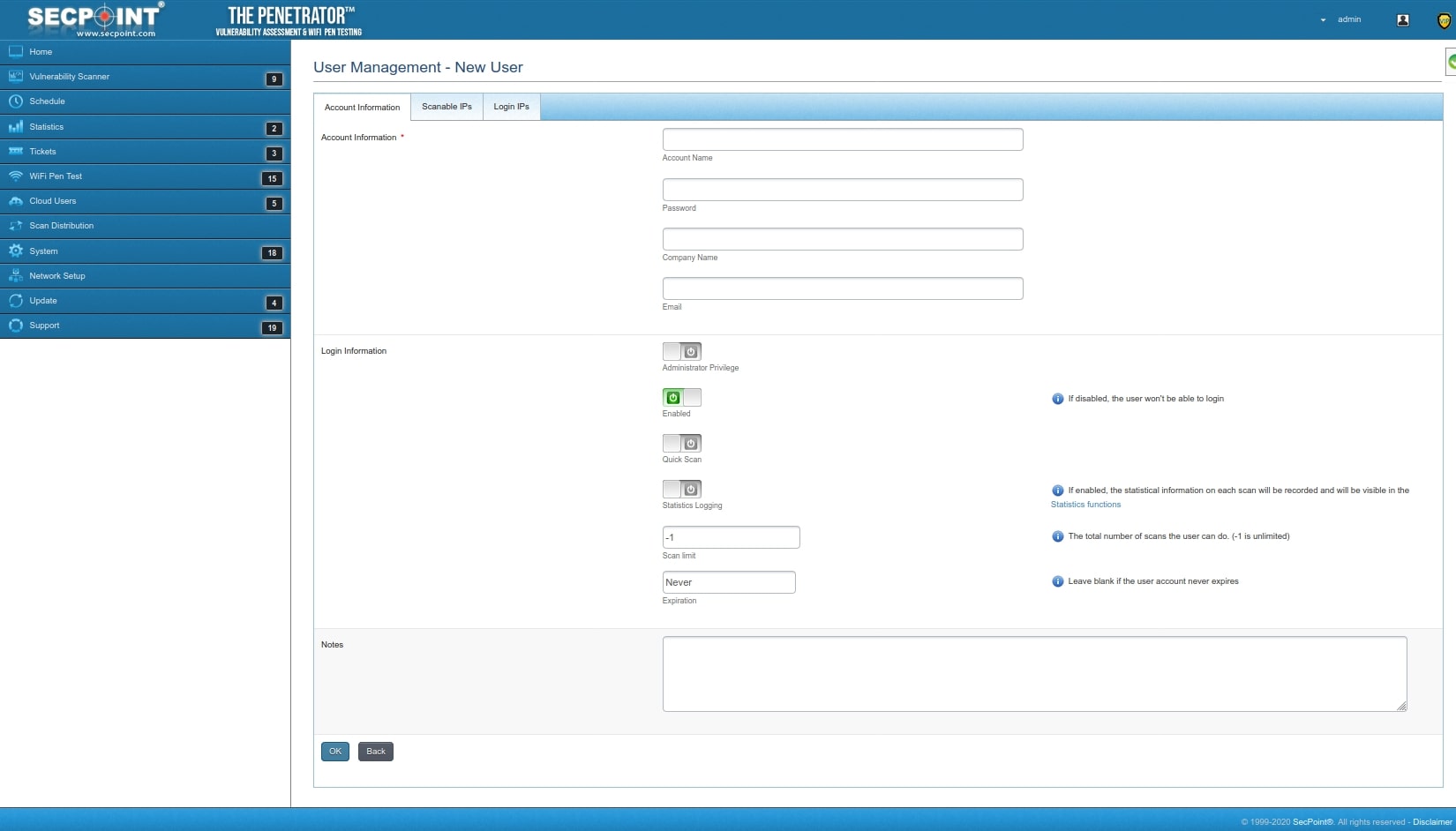
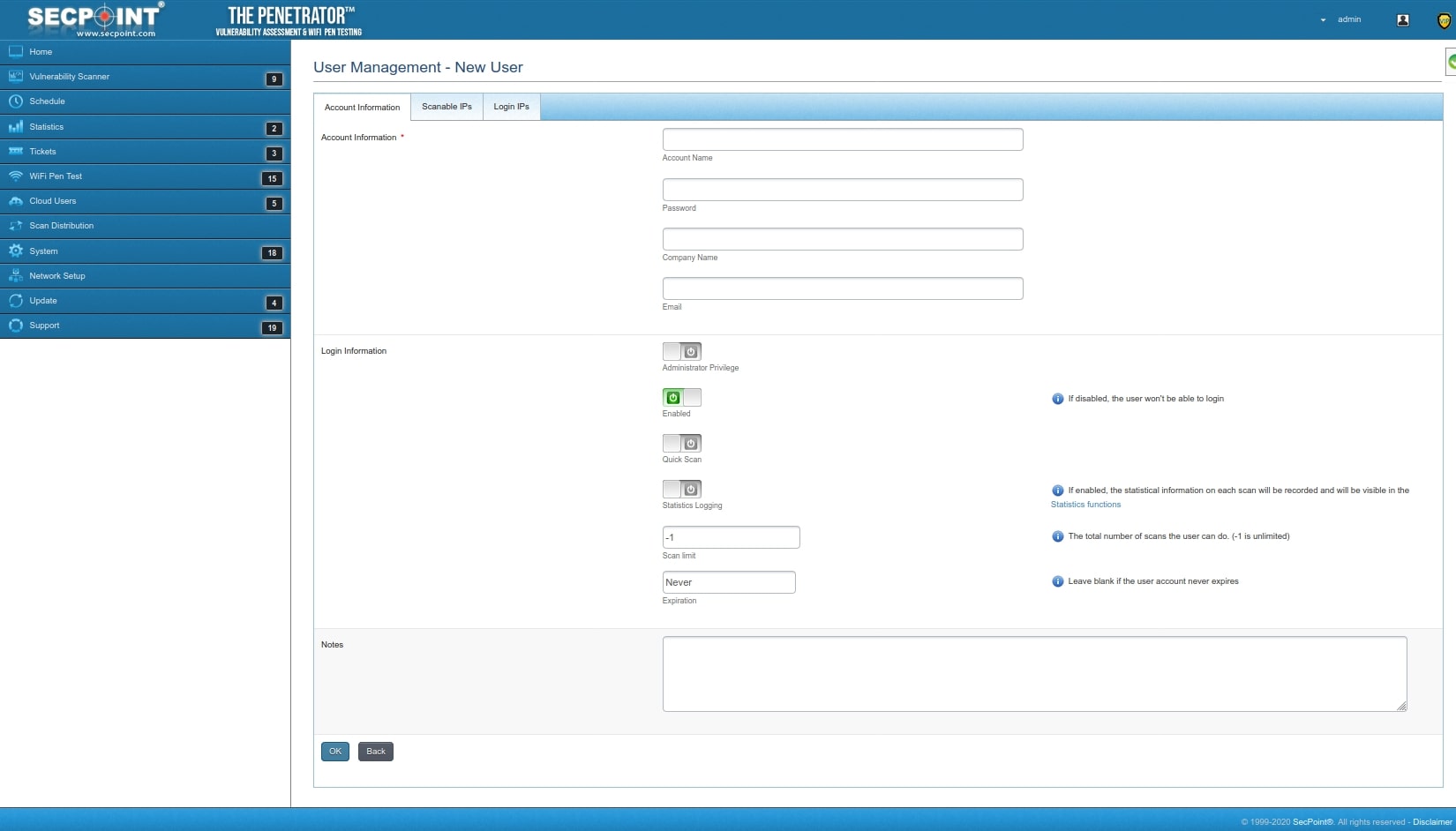
Different User Accounts for Vulnerability Scanning
Can you confirm, with different user accounts on the Penetrator, can one control which targets the users are allowed to assess? (either by IP or URL)
OR, can I only allow certain users to run certain pre-configured Vulnerability Scans?
Yeah you can do how you need.
Is it software version you have?
Difference Cloud and Software Vulnerability Scanner
What is difference between the penetrator software and the cloud penetrator? they seem to have the same functions?
The difference is that the Cloud Penetrator runs from https://penetrator.secpoint.com and can only scan Public IPs as a web service.
The software running in Cloud Penetrator and Penetrator software is the same.
With the Penetrator software you can deploy on a local laptop or server and then not just scan public IPs but also local IPs.
The Penetrator software also allows for reporting rebranding with Logo,Company name, Watermark which is not possible on the cloud version.
Vulnerability Scan with False Positives
After finishing the scan the status appears to be false positive. those it mean all scanned issue is false positive?
It means if the target system reply wrong codes back to the Penetrator.
example if you goto website
www.website.com/passwordfile
then the website must return 404 error code but sometimes websites turn wrong code 200 OK back.
When this happen you can send us the report and we make an intelligent learning in the Penetrator.
So it can recognize it in the future like a human and wont be fooled by it.
I would like a second Cloud Penetrator account
This is not possible now. If someone shares a scan, it will be shared with all the users in the system, so this is not something to do on cloud.
To do this, it's better to have a penetrator in house as software or appliance.
How to access ports
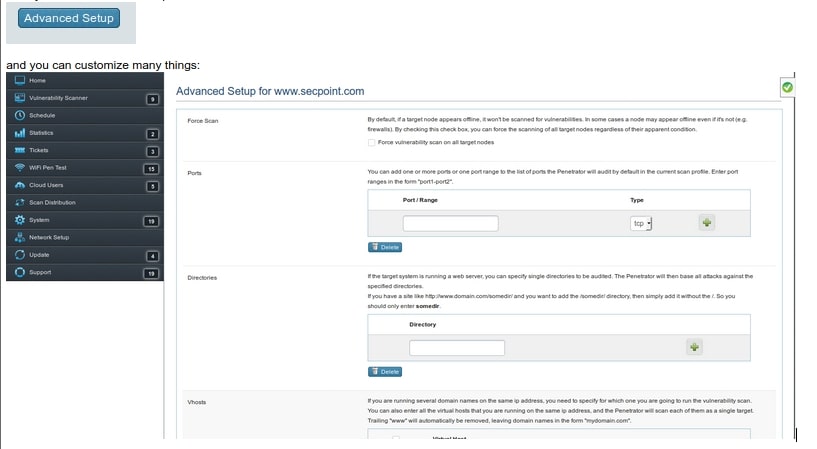
How can I access the ports from the advanced menu? Can you guide me please?
Sure you click advanced setup
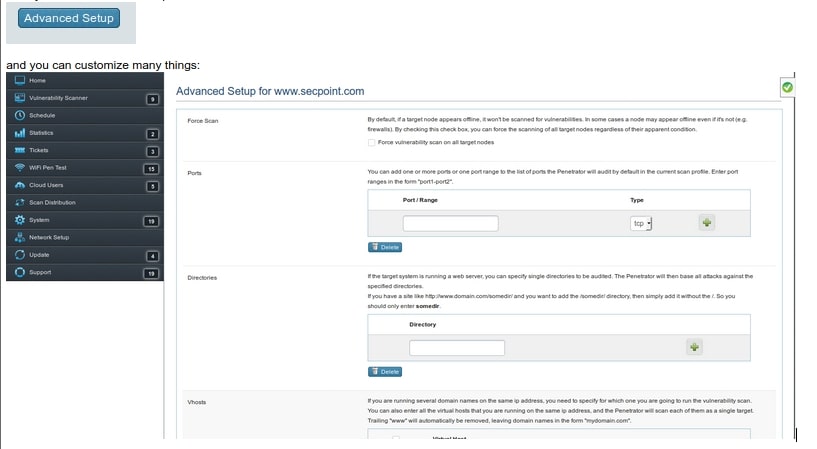
and you can customize many things:
Vulnerability Scan Scan Impact
I please need to understand if the vulnerability scan will corrupt or affect / change any of my systems or just look for holes
It is designed to be safe to scan.
It can scan production system with minimal to no network interference.
It has 9 profiles to choose between.
IP Pricing
Does the IP pricing for the Cloud Penetrator work the same as the Penetrator pricing? So a 1 IP license would scan unlimited IPs but only 1 concurrent IP?
On the Cloud Penetrator we need a permission form for each IP since it scan from our server.
I filled out the free vulnerability scan request but nothing happens
How can I change the company name displayed in the reports?
Please create a ticket on the ticket system and a support engineer will help you change it as fast as possible.
If my IP addresses changes how can I update my account?
If you need change your IP addresses please fill out the permission form and create a ticket for the support team to update it.
Can I scan local IP addresses with the Cloud Penetrator?
With the Cloud Penetrator you can only scan your Public IP addresses that our Cloud Scanner can see.
However you can just get the Penetrator software to scan your internal local IP addresses as well.
Please contact us for more information.
The Vulnerability Scanner gets blocked when scanning the Firewall
How can I avoid the vulnerability scanner Penetrator is getting blocked during scan?
When the Penetrator launches the vulnerability scan it will issue many attack forms that will trigger firewall IPS systems.
It is recommended to enable Shunning or white list the Penetrators IP address that it is scanning from to get an accurate result.
If you do not know how to do it please create a ticket on the support System.
Can I scan my local network from the Cloud Penetrator
How to Scan networks multiple locations
I want to scan my networks in multi locations remotely to see if any security issues we have that are open to hackers what do you offer that will do this?
Yes in this situation it is recommended to deploy the Cloud Penetrator Web Vulnerability Scanner.
It can scan all your public IP addresses for vulnerabilities.
Read more here about Cloud Penetrator.
How to scan for a Self Signed SSL cert?
Please use the Normal,Full or Web Scan Profile.
How to automatically scan your Public IPs
Find IP addresses for Vulnerabilities.
Virtual Hosts Vhost Web Security Scanning
Once you have been connected to the Cloud Scanner you type in your websites, domain names, virtual hosts or IP addresses to scan. You can easily scan a single IP address that has 100 Virtual Hosts Vhosts running on it. Then the Cloud Scanner can actually threat it as 100 individual sites.
This way you are not just scanning one IP address but actually scanning the Vhosts as individual sites.
Find your sensitive data leaked in to Search Engine
You might have sensitive data being shared on your website without even knowing it and even worse it might be indexed and cached in popular search engines.
Sign up to a free vulnerability scan in the right side menu.
Learn more about how you can scan your Public IP addresses.
You can choose between many profiles such as: Normal Scan, Extended Scan, Firewall Scan, Sans Top 20 Profiles and other compliance checks.
If your question is not in the list please mail us here.