The Protector Anti Spam UTM Firewall comes fully loaded with RBL customization
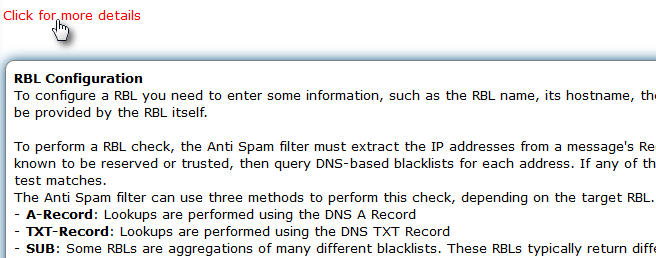
Reputation Block Lists, also referred to as "DNSBLs" or "DNS Blocklists", are external databases queried by the Protector during the Anti Spam analysis.
To perform a RBL check, the Anti Spam filter must extract the IP Address , then query RBLs for for each email and the message can be blocked as spam.
RBLs can be configured in menu Anti Spam > Black - White - Grey - RBL - TLD - Hardblock Lists.
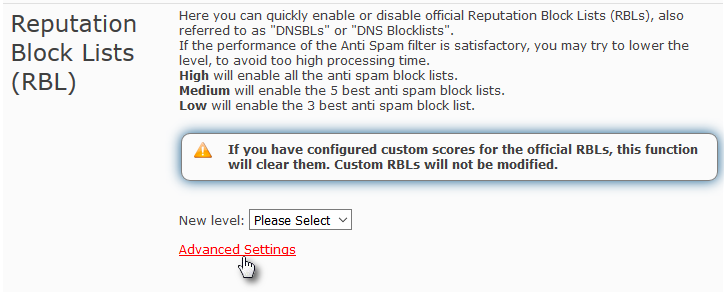
Here you can perform a quick configuration by selecting the New Level and/or go to Advanced Settings to configure each RBL individually.
When you set a new level, the Protector will enable/disable a pre-defined set of RBLs. You can then fine-tune RBLs through Advanced Settings.
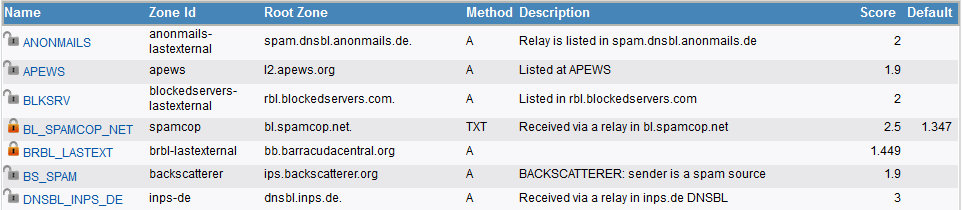
In this firmware each RBL is associated with a default score, which will contribute to the global score assigned to each email.
The default score can be changed depending on the reputation of the RBL itself and your experience with it (false positives etc.).
Positive scores are assigned to IP addresses with a bad reputation, negative scores are assigned to trusted IP addresses.
The score 0 will eliminate the use of a RBL.
You can see the result of RBL checks in the Message Details page of the Mail Archiver.
Here you can click on [ ] in the row of a Spam message and you will see the matching RBLs among the Message Details.
Spammers may use legitimate servers to send mail messages that contain links to bad websites.
In such cases these messages may not be caught by RBLs, and it’s possible to detect the message as spam through the analysis of the bad links contained in the message.
Bad links can be detected through external databases, named URI DNSBLs, that contain the domain names or IP addresses found in the clickable links of a spam message.
In this firmware we have added the possibility to enable/disable this check.
This function is available through menu Anti Spam > Black - White - Grey - RBL - TLD - Hardblock Lists.
Here you can enable/disable this option by simply clicking on Active (checked by default).
When this option is enabled, the Protector will extract all URIs from a message and check them against a list of URI DNSBLs.
If the match is positive, the message can be blocked as spam even if the sending IP for that spam is not listed on any RBL (see the RBL feature).
The external databases to which the Protector will connect, usually provide a free service for a limited number of requests.
When this number exceeds, the database will not perform the check and a special tag is added to the message header, in "X-Spam-Status". Possible tags are: "URIBL_BLOCKED" for database uribl.com or "SURBL_BLOCKED" for surbl.org.
URIDNSBL tags added to messages are visible in the Message Details page of the Mail Archiver.