Portable Penetrator Extended Frequently Asked Questions FAQ
You can find more questions in the right side menu.
Learn about Extended questions for Portable Penetrator.
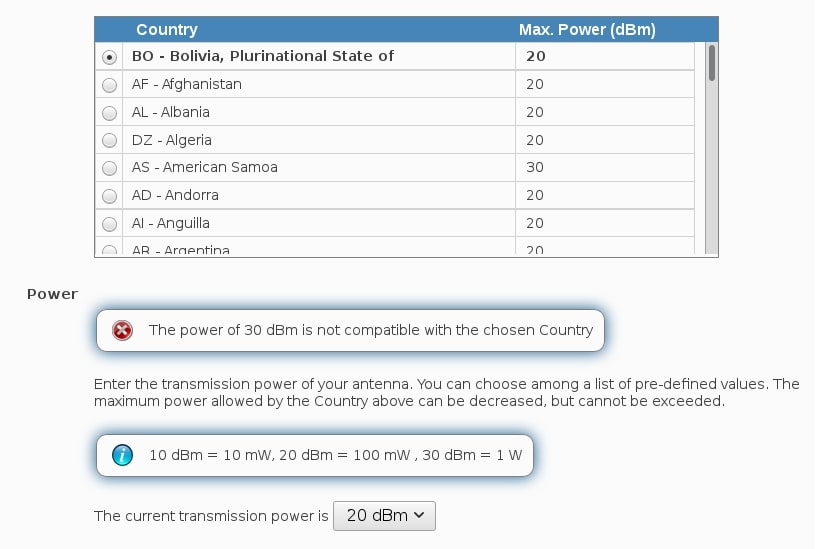
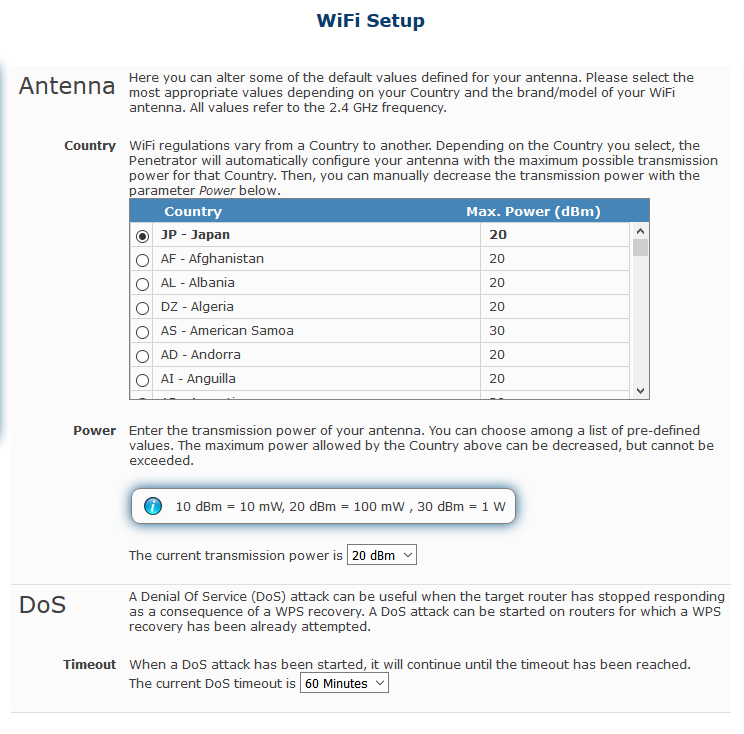
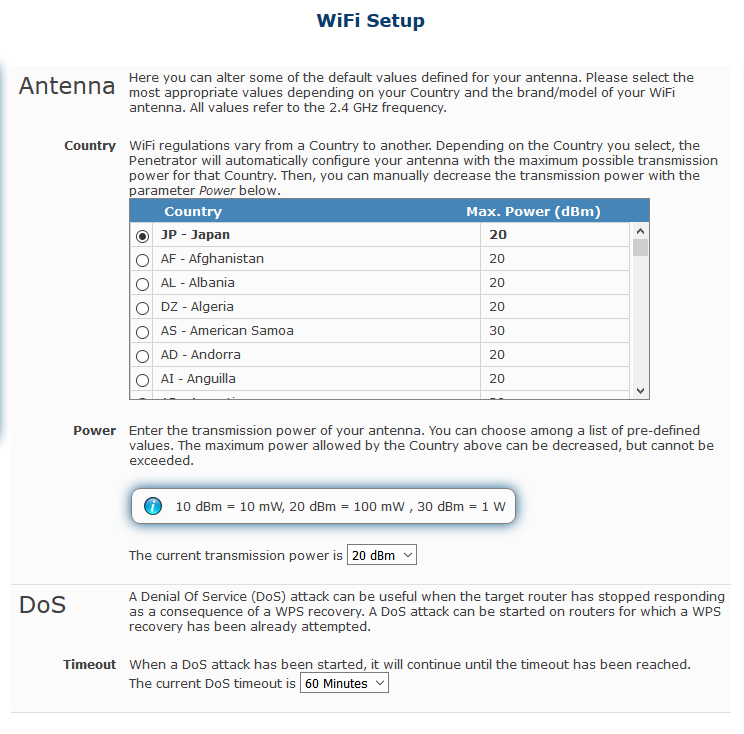
How to set 30 dBm?
I have the Alfa awus036h and in my secpoint admin I have my country set to Dominican Republic 30dBm but on the right corner of the screen it always says "Wifi power: 20dBm medium"
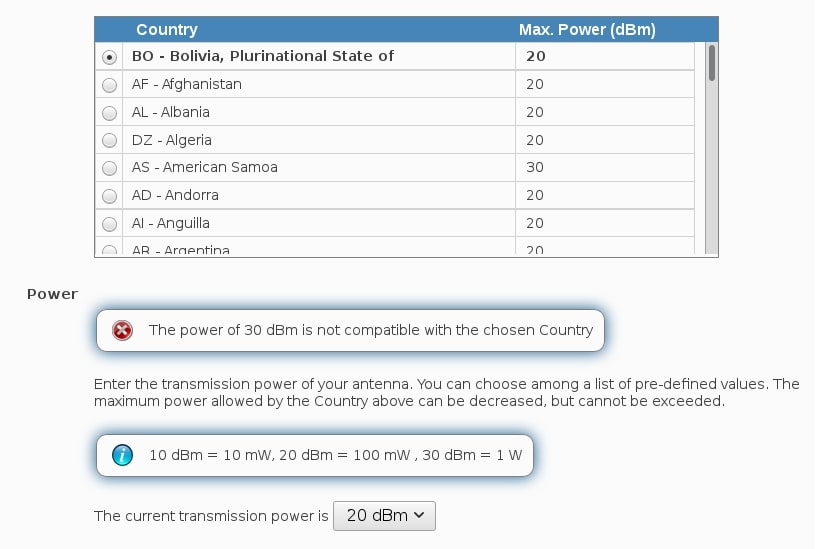
I have tested on 64 bit, and Bolivia has max power 20dBm, not 30dBm. So it is normal that he can't set it to 30 dBCan this software crack WiFi? m, because it will give an error, see the picture. To set 30 db, use Belize
I have no difficulties in setting any country with 30 dbm. American Samoa, Bolivia or other countries
This can be things as how to recover WPS pin code
How to setup and configure the software.
How to recover WPA WPA2 keys.
How to connect the Wireless adapter on Windows 7, Windows 8 and Mac OS X.
Size of files?
I have an issue with size of files.
Portable Penetrator was installed on a machine that has only Windows 7.
It has used 158 GB. Is this normal?
No it is not normal it should be only the installed size and 158 gig maximum size.
One I have here on a Windows 10 is about 20 GB
Which WiFi Encryption Recovery Method must I choose?
To learn more about the different WiFi encryption types and best recovery technique please see the recovery guide:
WiFi Pen Testing Software Here
How can I hack WPA 2 Password?
What is the best way to perform a penetration test on a WPA 2 password to see if my WiFi Access point is secure?
With the Portable Penetrator professional WiFi Pen testing software it is possible to audit WiFi Access points. You can perform real WiFi penetration test to recover the WPA 2 Password in order to see if you are vulnerable to hacker attacks. It uses the same techniques like a black hat hacker would use but in a controlled environment.
Do I have to have Internet service in order to use this program?
No not required.
How complicated is it to use?
It is an advanced tool for penetration yet an easy to use GUI interface.
How does High Speed Cracking service work?
Hey! One quick question…
Hey! One quick question… which one is the best password file, when you know the password is alphanumeric and it starts with 89 or 90 and can be several numbers/characters long?
Best is to run all of them.
You can also add your own lists.
Portable Penetrator WiFi Cracking Drivers
I get the Portable Penetrator, now when I try to install the drivers carad on windows 10 I get the message is not compatible with this windows version.
In Windows 10 you must not install any drivers.
The only thing to install is VMware Player or VMware Workstation.
Then you load the Portable Penetrator Image which contains its own linux distribution with build in drivers.
Once it is loaded up you goto USB devices and connect the WiFi Adapter RTL8187L from WIndows to the VMware container.
Then it will have all drivers inside.
Please let know if it works.
Thanks.
It looks correct in image it is connected the RTL8187L.
This antenna is only for wifi pen test not to connect to internet
So next step is to login to the software
Please see install guide:
Do we need a laptop to run it?
Question about Portable Penetrator. do we need a laptop to run it? what is the hardware requirement if we need to have a laptop.
You can run it on both a desktop or laptop computer.
It is recommended minimum I3 cpu or higher and minimum 2 Gb ram or higher.
Minimum Portable Penetrator Requirements
Could you please inform us the minimum hardware requirements for the Portable Penetrator Virtual software licenses in the attachment?
SP-PP2000-1-SW-1YB
SP-PP2000-2-SW-1YB
SP-PP2000-4-SW-1YB
SP-PP4000-8-SW-1YB
SP-PP6000-16-SW-1YB
SP-PP6000-32-SW-1YB
SP-PP6000-64-SW-1YB
SP-PP6000-128-SW-1YB
SP-PP6000-256-SW-1YB
SP-PP6000-512-SW-1YB
SP-PP6000-1024-SW-1YB
SP-PP6000-UNL-SW-1YB
1-4 IP = I3, 2 gb ram
8-64 IP = I5 2 core, 4 gb ram
128-256 = I7 4 core 8 gb ram
512-unl = i7 4-8 core 8 gb ram
Question about Portable Penetrator laptop requirement?
Question about Portable Penetrator. do we need a laptop to run it? what is the hardware requirement if we need to have a laptop.
You can run on any laptop with I3 or great CPU platform.
How can I unrar the files on Mac OS X?
Hi
Please use
https://www.rarlab.com/download.htm
Problem to load Penetrator in VMware Player
I have downloaded the following and unpacked the files.
the filenames are:
Penetrator-hyper-v-14.2-64bit-march2018.part01.rar
Penetrator-hyper-v-14.2-64bit-march2018.part02.rar
Penetrator-hyper-v-14.2-64bit-march2018.part03.rar
But they wont load in VMware Player.
Please make sure you load the Player version as seen below
Do you have the 3 same files?
Best WiFi Adapter?
What is the common wifi adapter that we can offer, to be used in pentesting?
Most use:
Alfa AWUS036H rtl8187L
or
TPLink TL-WN722N
or
Alfa AWUS036NHA AR9271
AWUS036NHA WiFi Password Recovery Chipset AR9271All low cost and available most places.
Which WiFi USB adapter can I use?
AWUS036H
and
AWUS036NHA (black one)
Also TP LINK WN722H can work.
https://www.secpoint.com/wifi-usb-adapters-performance-test.html
I cant unpack the downloaded files please help
I’m trying to install the software uncompressing the 3 parts downloaded but I’m just able to uncompress the first one, and when I try to uncompress the second it doesn’t work, showing the following error:
Please use Winrar then it will work.
WEP only encryption break
Do i need a separate HW adapter or is the built in Intel AC 8620 enough?
You need Alfa with realtek 8187L RTL8187L
Other chipsets can also be used.
Please see
https://www.secpoint.com/wifi-usb-adapters-performance-test.html
What is difference on PP versions?
Hello, I would like to know what is the Light version on PP
specifically, what are the differences between light and full?
The Light Version can only do WiFi Pentesting.
Where the full version also can do Vulnerability Scanning & Assessment.
Windows 10 64 Bit
I have a windows 10 64 bit do I need to run a vm ware program and how much space do I need
Yes you must run VMware since it is a linux running.
You can download VMware player v15.0
https://filehippo.com/download_vmware-workstation-player/
How can I crack a WiFi Network if all methods failed
In a WiFi Pentest I have tried word list attack, WPS attack, Pixie Dust attack on my client WiFi Access point and it seems to be secure and protected from those attacks.
I want to make sure it cant be broken in to are there other techniques I can use as well?
Another approach more sneaky attack is doing a WiFi Phishing attempt.
In that case you choose an remote access point. The Penetrator knock it offline and clone its MAC address to make a new Access Point with the same name as a target while the target is being knocked offline.
When it looks as the target access point and being online pretending to be it. Legitimate users will connect to it.
When they are connected it will then try to trick them to reveal the WiFi password by pretending to be a new firmware update that must be installed.
This technique rely on the vulnerability in the human instead of the access point.
It can produce high success rate by fooling the humans to reveal their real passwords easily and fast.
The only downside is the attacker must be in the area waiting for users to connect and must be in the close by area to produce a good enough signal for users to connect to the spoofed clone access point.
Where in a normal traditional WiFi connection handshake attack the attacker can just sniff a handshake and go to another location and run large word list cracking on it.
Can it do offline wifi attack also?
Yes internet connection is not required.
What to do if wordlist attack fails?
If you dont succeed to crack a network it shows the network is secure in that case.
When doing a pen testing you can document you did several attacks on it and it withstand it.
When you do an assessment on a remote WiFI access point several factors such as router brand, signal strength, encryption used, security updates on the remote access point.
We use the latest techniques for the attacks and when new attacks get revealed we add those quickly.
That is why the rapid update cycle on the software.
Please study all the FAQ with answered questions here
https://secpoint.zendesk.com/hc/en-us/sections/115000166289-Portable-Penetrator-F-A-Q
We already include large wordlists in the software you can upgrade to in the menu.
You can use your own list as well if you have some more specific list.
Now another approach is the one you also mention they are already working on a similar way which is very sneaky.
In that case you choose an remote access point. The Penetrator knock it offline
The challenge is if it can be done with only 1 wifi adapter or if more are needed.
Then it spoof the access point and you must wait for users to connect.
This way it will trick valid users to connect to it and ask them to reveal their password for an update.
Different WiFi Frequency for Pen Testing
What is the difference on all the Wireless Standards including 802.11a, 80211b/g/n, & 802.11ac
Which one to choose and is best for WiFi wireless penetration testing?
The explanation of 802.11 WiFi Family Standards for Penetration Testing:
Frequency
IEEE 802.11bgn = 2.4GHz only
IEEE 802.11gn = 2.4GHz only
IEEE 802.11agn = 2.4GHz 5GHz
IEEE 802.11ac = 2.4GHz 5GHz
abgn
Macbook Pro WiFi Antenna
Can i use my macbook pro wifi antenna to scan wifi channels around me instead of buying an external antenna?
You need the external USB Alfa WiFI Adapter to do injection and packet sniffing.
Online Question
Hi do the wifi penetrator software need internet to work or does it work offline?
No
No internet connection is required for operation.
It works offline.
It only needs Internet to activate license and upgrade to latest firmware.
WiFi adapter to use?
In regards to the WiFi penetrator, it says on your website that it’s compatible with Alfa AWUS036H
Is it also compatible with the newer Alfa Adapters?
There are a lot!
AWUS036ACH
AWUS1900
AWUS036NHA
AWUS036NH
Please let me know if it’s compatible with all these Alfa adapters or not?
Reply:
the problem is many adapters have a locked chipset from the factory.
We need a chipset that is open for packet injection and raw monitor mode to capture packets.
One of the favorite adapters for this purpose is the older but very powerful AWUS036H with the RTL8187L chipset.
This adapter is the best.
You can try the awus036nh depending on chipset it might work.
But it is recommended to use the awus036h with rtl8187l
You can find the rtl8187l chipset devices in ebay (beware many fake from china) and we also provide them.
The full edition what means the IP license?
Am I only scan one specific IP address
It means in full version you can do vulnerability scanning as well.
1 IP means 1 IP concurrent.
So if you need to scan 100 IPs it will queue them and scan 1 IP at a time.
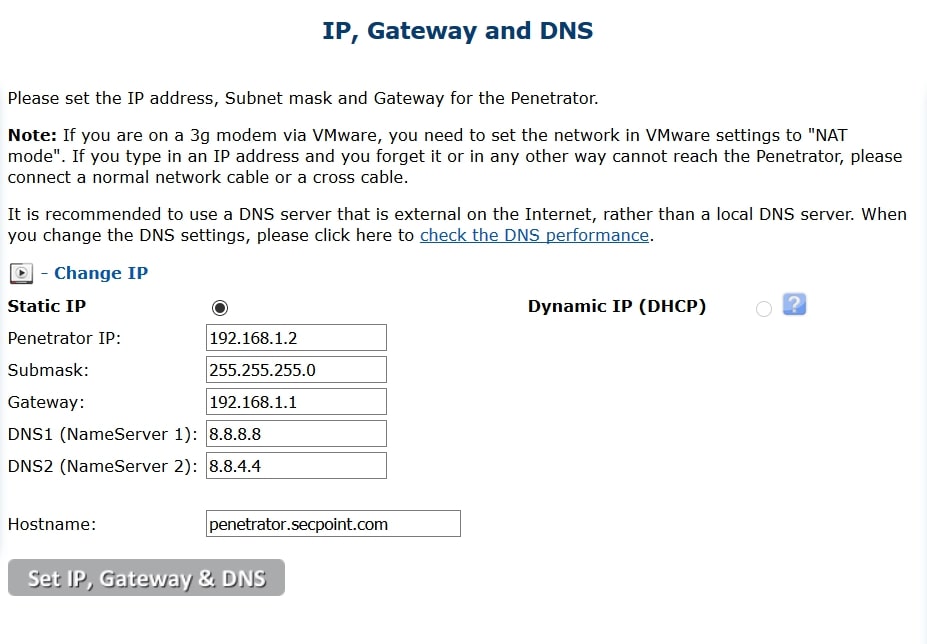
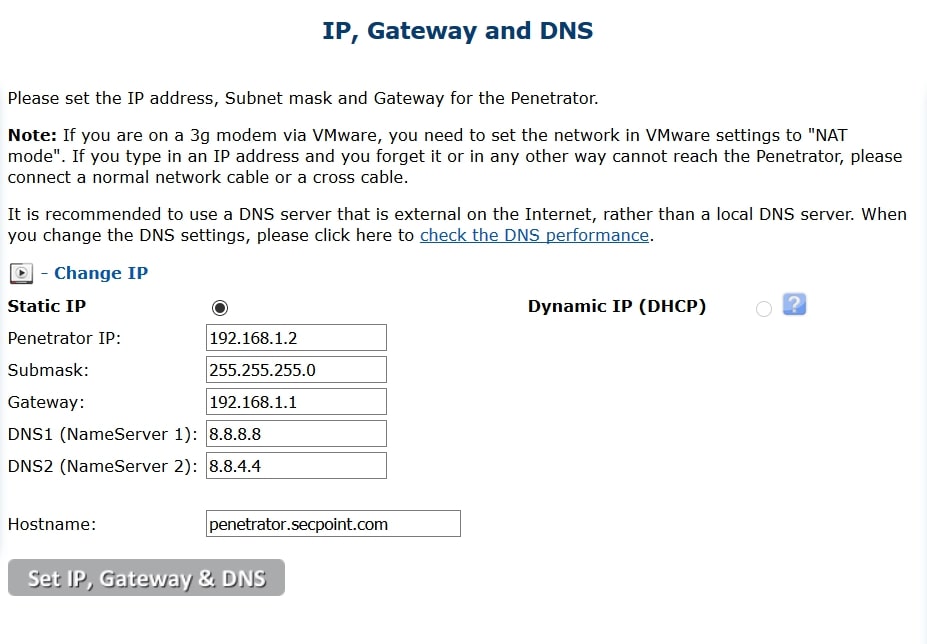
How to get online?
When you start up the Portable Penetrator and goto the network menu.
It might be set at a default IP address of 192.168.1.2.
Here you need to click the DHCP mode.
To have the option clickable for security you must login to the penetrator to https://127.0.0.1/
Where can I find the WiFi Adapter Compatability Guide?
AWUS051NH V2
I would like to know your new wifi adapter of AWUS051NH V2.
New wifi adapter can use WEP cracking. I check up internet.
It does not transmit injection packet. When I buy new wifi, Do I introduce
new driver?
It can inject packets.
There can be some difficulty to capture connection handshakes in different situations.
Please make sure it is latest firmware and 64 bit.
Latest firmware is 38.2.9 has wifi driver updates.
Latest WiFi Guide:
https://www.secpoint.com/wifi-usb-adapters-performance-test.html
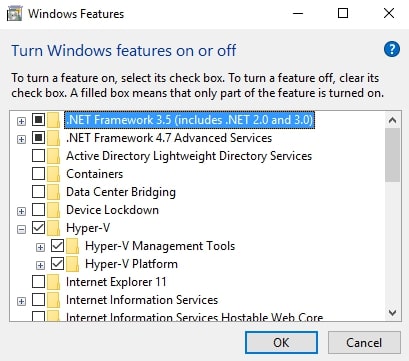
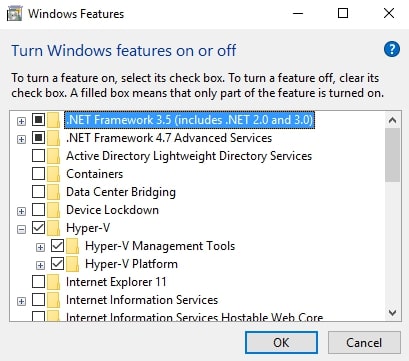
Disabling Device/Credential Guard
I am getting this error about not being compatible problem when trying to start VMware Player.
Solution
You must disable Hyper-V from Windows Features:
From the windows search type in Enable Disable features
Find the Hyper-V and unclick it.
You might need to reboot afterwards.
5GHz WiFi Pentesting WPA WPA2 WPS
Do you have USB adapter to see complete 5.8GHZ range frequency channel 5180 MHz 5185 MHz 5190 MHz 5195 MHz 5200 MHz
secpoint Eng
5205 MHz 5210 MHz 5215 MHz 5220 MHz 5225 MHz
5230 MHz 5235 MHz 5240 MHz 5260 MHz (DFS) 5265 MHz (DFS)
5270 MHz (DFS) 5275 MHz (DFS) 5280 MHz (DFS) 5285 MHz (DFS) 5290 MHz (DFS)
5295 MHz (DFS) 5300 MHz (DFS) 5305 MHz (DFS) 5310 MHz (DFS) 5315 MHz (DFS)
5320 MHz (DFS) 5325 MHz (DFS) 5480 MHz (DFS) 5485 MHz (DFS) 5490 MHz (DFS)
5495 MHz (DFS) 5500 MHz (DFS) 5505 MHz (DFS) 5510 MHz (DFS) 5515 MHz (DFS)
5520 MHz (DFS) 5525 MHz (DFS) 5530 MHz (DFS) 5535 MHz (DFS) 5540 MHz (DFS)
5545 MHz (DFS) 5550 MHz (DFS) 5555 MHz (DFS) 5560 MHz (DFS) 5565 MHz (DFS)
5570 MHz (DFS) 5575 MHz (DFS) 5580 MHz (DFS) 5585 MHz (DFS) 5590 MHz (DFS)
5595 MHz (DFS) 5600 MHz (DFS) 5605 MHz (DFS) 5610 MHz (DFS) 5615 MHz (DFS)
5620 MHz (DFS) 5625 MHz (DFS) 5630 MHz (DFS) 5635 MHz (DFS) 5640 MHz (DFS)
5645 MHz (DFS) 5650 MHz (DFS) 5655 MHz (DFS) 5660 MHz (DFS) 5665 MHz (DFS)
5670 MHz (DFS) 5675 MHz (DFS) 5680 MHz (DFS) 5685 MHz (DFS) 5690 MHz (DFS)
5695 MHz (DFS) 5700 MHz (DFS) 5705 MHz (DFS) 5710 MHz (DFS) 5715 MHz (DFS)
5720 MHz (DFS) 5745 MHz 5750 MHz 5755 MHz 5760 MHz
5765 MHz 5770 MHz 5775 MHz 5780 MHz 5785 MHz
5790 MHz 5795 MHz 5800 MHz 5805 MHz 5810 MHz
5815 MHz 5820 MHz 5825 MHz 5830 MHz 5835 MHz
5840 MHz 5845 MHz 5850 MHz 5855 MHz 5860 MHz
Try
Alfa AWUS051NH V2
Find Hidden SSIDs
I was under the impression you had software that could find and identify the name of hidden SSIDs?
Yes we have Portable Penetrator.
https://www.secpoint.com/portable-penetrator.html
Frozen GUI how to Reset?
When i open the program for some reason i cannot open any browser nothing works.
Having an issue with getting penetrator to launch. I just updated VM workstation and now it doesn't seem to let me lunch firefox to get the penetrator started.
Please press CTRL ALT BACKSPACE all 3 at the same time to reset the GUI interface.
Which Web Browsers are supported by the Penetrator?
It comes with Chromium, Firefox, Opera, TOR.
For the Portable WiFi Penetrator what is the success rate ?
It depends on few factors including:
- Strength of target WiFi.
- Type of Encryption used WEP WPA WPA2 WPS.
- Sophistication of Encryption used.
- Frequency 2.4 GHz / 5 GHz.
- Quality of WiFi Adapter.
- Power of computer being used.
- Quality of Word Lists.
Can this software crack WiFi?
The Portable Penetrator along with the correct WiFi Adapter perform WiFi Penetration Testing and recover WPA WPA2 WPS WEP Keys.
Do TP-Link TL-WN722N work with the Penetrator?
Yes it works in 32 bit and 64 bit editions that you can Capture WPA/WPA2 handshakes and WiFi Scanning.
It is recommended to mount heat sinks on it.
The range is very poor compared to rtl8187l Alfa AWUS036H device but it still works.
Example to use some Raspberry Pi heat sinks.

Issue to Launch GUI interface
Having an issue with getting penetrator to launch. I just updated VM workstation and now it doesn't seem to let me launch firefox to get the penetrator started.
Can you press CTRL ALT BACKSPACE All 3 buttons at once.
Is Internet Connectivity required during operation?
For wifi key recovery software needs Internet or not ? can i use this without Internet?
It only need internet to activate and get updates otherwise it is not needed.
VMware Authorization service not running how to fix it?
1: run services.msc
2: Find VMware authorization service in list and right click and enable
I cant get online in VMware NAT or Bridged mode
Have you set Vmware to NAT or Bridged mode?
Yes But I cant get online.
Please download the How to get online guide here.
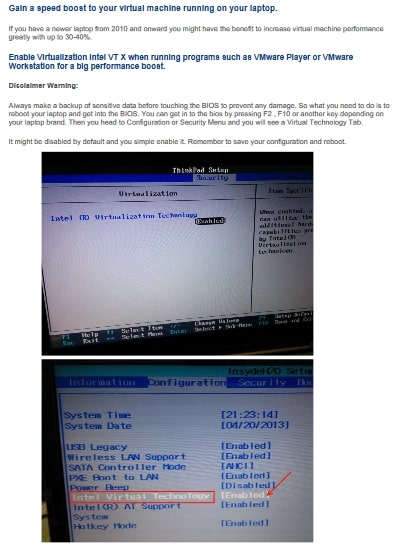
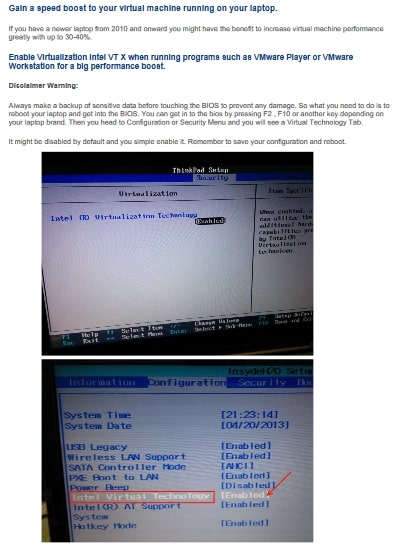
How can I enable Virtualization Support on my Laptop?
Please follow the guide below:
Binary Translation Error
Binary translation is incompatible with long mode on this platform. Long mode will be disabled in this virtual environment and applications requiring long mode will not function properly as a result
I am getting this error:
Binary translation is incompatible with long mode on this platform. Long mode will be disabled in this virtual environment and applications requiring long mode will not function properly as a result. See http://vmware.com/info?id=152 for more details.
VMware Player unrecoverable error: (vcpu-0)
vcpu-0:VERIFY vmcore/vmm/main/cpuid.c:386 bugNr=1036521
A log file is available in "C:UsersuserDownloadsPENETRATOR-VMPlayer-OS-14.2-64Bit-Jan17vmware.log".
It means you are running the 64 Bit version on a 32 Bit platform.
You can upgrade your system to a 64 Bit or download the 32 Bit version of Portable Penetrator to fix it.
Trial Software version?
Hi, is there any way i can trial this software before I purchase it? Or at least watch a demo to see it in action. I have watched the YouTube video and I am still not sure. Thanks
You can mail [email protected] to hear more about trial option.
Trial is only possible for business customers.
How do i increase the power it is only running at 20dbm ?
If you click WiFi Menu and Setup
You can customize it here.
Do you provide a wordlist with the Portable Penetrator?
Yes.
It comes with 12 word lists total of 1.1 Billion entries.
WPA2 Router Crack
Can your product crack wps wpa-2 router? my router is very secure ans usually locks after failed attempts and stop times it just says "failed to associate" can your product crack it?
It depends on encryption deployed, router brand and protection level.
If you already secure your router it might be harder to crack it.
There is no guarantee when doing password recovery.
It uses the latest techniques for cracking a long with word list cracking process.
Whats the difference between using your Portable Penetrator & Kali linux
There are several differences depending on your requirements:
The Portable Penetrator comes with an an easy to use GUI interface with professional reporting.
And you operate with the GUI.
You can do customized reporting add your own company name and logo.
It can do Vulnerability Scanning and Vulnerability Assessment.
Comes preloaded with 1 billion entries word lists.
Automatically updated 64 Bit Images easy to download.
Live chat and helpdesk support included.
How do I correctly connect the external WiFi USB Adapter?
How can easily connect my external WiFi USB Adapter to perform WiFi Pen testing?
How to disconnect session after WiFi Crack
I would like to know if its ok to disconnect the antenna after capturing the handshake and starting a wpa /wpa2 scan
As long as you have the handshake you can go to another location and also disconnect antenna?
How to update VMware Tools?
How can I install or update the VMware tools in my Portable Penetrator software?
My VMware tools is oudated or missing how can I install it?
Please contact our l live chat or create a ticket here to get help from our support engineers.
Do you have a Cloud WPA Cracker?
My Computer is to slow for cracking WPA WPA handshake file.
Do you offer a Cloud Cracker service with much higher speeds?
Yes we have the CLOUD WPA CRACKER service with high capacity cracking.
Click here for more information
How to Capture WPA WPA Handshake
How can I copy a captured WPA/WPA2 handshake to a flash drive to use on another computer?
You can simple insert a flash drive to the Portable Penetrator installation.
A new drive will pop up wher eyou can easily copy files.
It is recommended to format it fat32 for it to be compatible.
How to use custom WPA PWA2 wordlist file
Is it possible to upload my own custom word list for WiFi Cracking on the Portable Penetrator?
Yes.
You can generate custom word lists for cracking WPA WiFi Handshakes on the Portable Penetrator.
You can also upload your own word lists files easily.
The word list files need to be placed in /home/apps/wordlist/languages/ for the Portable Penetrator interface to be able to utilize it.
Can only WiFi Adapter be used?
Does the Portable Penetrator WiFi Cracking software only work with Alfa WiFi Adapter antenna install the vm player on a windows 10 64k machine automatically or do I need to do a separate install?
It works with any supported chipset and includes many different WiFi brands including and not limited to Alfa, TP-Link, Realtek and more.
When you install VMware Player or Workstation on Windows 10 the drivers will automatically be loaded.
What is best way to get online?
How to get Online with the Virtual Portable Penetrator?
There can sometimes be difficulty with VMware Player or Workstation under Windows 10 to get online via NAT or Bridge mode.
This can be caused by that the VMware Player or Workstation uses the wrong NIC Network interface card.
Example on the laptop you are connected to the Internet with the build in WiFi adapter but VMware still uses the LAN port even if it is not connected.